Cybersecurity •
Feb '26
Phishing scams have become a persistent threat to internet users, with tactics evolving each year. Today, attackers are using more sophisticated methods, making it essential for individuals and organizations to stay informed and vigilant. The growing... << Continue >>
Cybersecurity •
Feb '26
Cybersecurity threats have evolved rapidly, pressing enterprises to rethink how they safeguard sensitive data, maintain business continuity, and protect their reputation. The past year has seen a surge in both the frequency and sophistication of atta... << Continue >>
Cybersecurity •
Feb '26
Cyber threats have become a constant concern for individuals and organizations. With more personal and business activities moving online, the risks associated with data breaches, ransomware, and other cybercrimes are growing. Many people are now aski... << Continue >>
Cybersecurity •
Feb '26
Imagine walking into a modern office. The lights adjust automatically as you enter, the coffee machine starts brewing your favorite blend, and the conference room screens light up, ready for your presentation, all without anyone lifting a finger. Thi... << Continue >>
Cybersecurity •
Feb '26
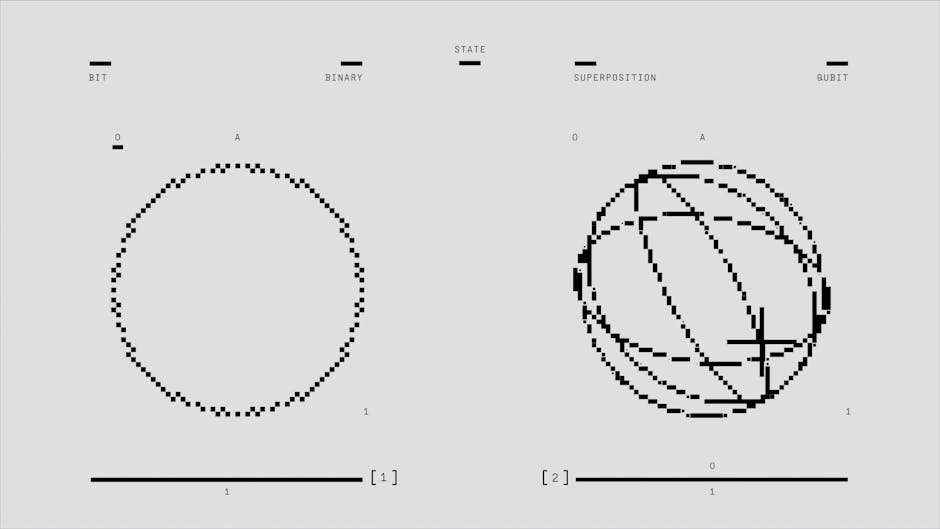
Quantum computing is rapidly moving from theoretical research into practical application, raising important questions about Unlike classical computers, which process information in binary bits, quantum computers use quantum bits (qubits) that can ex... << Continue >>
Cybersecurity •
Feb '26
Building a strong cybersecurity culture within an organization is not just about deploying the latest firewalls or antivirus software. It’s about shaping behaviors, attitudes, and shared values that prioritize security at every level. Employees are... << Continue >>
Cybersecurity •
Feb '26
The NIST Cybersecurity Framework stands as a benchmark for organizations aiming to strengthen their information security posture and meet compliance requirements. Developed by the National Institute of Standards and Technology, this framework offers ... << Continue >>
Cybersecurity •
Feb '26
Remote work has rapidly shifted from a niche arrangement to a standard practice for businesses of all sizes. While this flexibility offers many benefits, it also introduces new cybersecurity risks that can threaten both individuals and organizations.... << Continue >>
Cybersecurity •
Feb '26
Zero Trust security has become a central topic for organizations seeking to protect sensitive data and maintain operational integrity. The traditional approach of trusting users or devices inside a corporate network has proven insufficient, especiall... << Continue >>