Quantum Computing and the Future of Encryption
Quantum computing is rapidly moving from theoretical research into practical application, raising important questions about Unlike classical computers, which process information in binary bits, quantum computers use quantum bits (qubits) that can exist in multiple states simultaneously. This unique capability allows quantum machines to solve certain problems much faster than traditional computers, particularly those involving complex calculations like factoring large numbers, a cornerstone of current encryption methods. As researchers and technology companies make significant progress in building more stable and scalable quantum systems, the potential impact on cryptography and data privacy is becoming a pressing concern for individuals, businesses, and governments alike.
Understanding Quantum Computing: Fundamentals and Progress
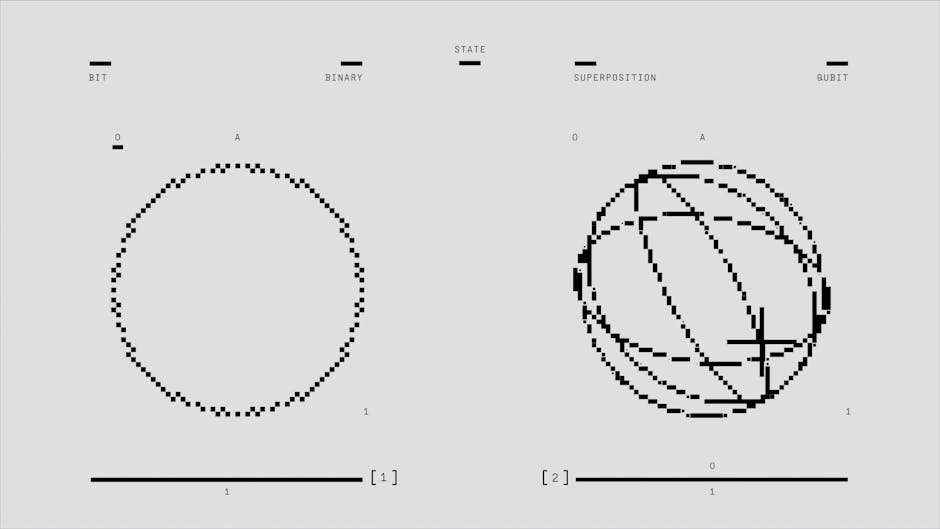
Quantum computing is grounded in the principles of quantum mechanics, a field that describes the behavior of matter and energy at the smallest scales. Qubits, the basic units of quantum information, can represent both 0 and 1 at the same time due to a property called superposition. Additionally, qubits can be entangled, meaning the state of one qubit is directly linked to another, regardless of distance. These properties allow quantum computers to process vast amounts of information in parallel, making them exceptionally powerful for specific tasks.
Over the past decade, advancements in quantum hardware have accelerated. Companies like IBM, Google, and startups such as IonQ have developed quantum processors with dozens of qubits, and some have demonstrated "quantum supremacy", the ability to solve problems beyond the reach of classical computers. However, these machines are still in their early stages. Quantum systems are highly sensitive to environmental noise and require sophisticated error correction techniques to maintain stability during computations.
Despite these challenges, investment in quantum technology continues to grow. Governments in the United States, China, and Europe are funding research initiatives aimed at achieving practical quantum computing within the next decade. This momentum is driving both excitement and anxiety about how quantum breakthroughs will reshape industries reliant on secure digital communication.
| Year | Quantum Computing Milestone |
|---|---|
| 1994 | Shor’s algorithm for factoring large numbers proposed |
| 2019 | Google claims quantum supremacy |
| 2022 | IBM unveils 127-qubit Eagle processor |
| 2023 | IonQ demonstrates error-corrected logical qubits |
Encryption Today: How Data Stays Secure
Modern encryption relies on mathematical problems that are easy to perform in one direction but extremely difficult to reverse without a secret key. The most widely used method for securing online data is RSA encryption, which depends on the difficulty of factoring large prime numbers. Another common approach is elliptic curve cryptography (ECC), which uses algebraic structures over finite fields to create secure keys.
These encryption schemes are foundational to online banking, private messaging, and secure government communications. They protect sensitive data by making it computationally infeasible for attackers to break the code using current technology. Even with powerful supercomputers, cracking a 2048-bit RSA key would take thousands of years using brute force methods.
However, these systems are not immune to future threats. Quantum computers have the potential to solve the mathematical puzzles underlying RSA and ECC much more efficiently than classical computers. This vulnerability has prompted cryptographers and security experts to rethink how we protect digital information in a world where quantum attacks could become feasible.
The Quantum Threat: Breaking Traditional Encryption
The main concern with quantum computing’s rise is its ability to undermine widely used encryption algorithms. Peter Shor’s algorithm, introduced in 1994, showed that a sufficiently powerful quantum computer could factor large numbers exponentially faster than classical machines (nature.com). This breakthrough means that once quantum computers reach a certain scale and reliability, they could decrypt data protected by RSA or ECC in a matter of hours or days.
This looming threat has significant implications for personal privacy, corporate security, and national defense. Sensitive information intercepted today could be stored and decrypted later when quantum computers become available, a tactic known as "harvest now, decrypt later." Organizations handling confidential data must consider not only current risks but also future vulnerabilities as quantum technology advances.
It’s important to note that not all encryption is equally vulnerable. Symmetric-key algorithms like AES are more resistant to quantum attacks but would still require longer keys to maintain their security level. The urgency lies in transitioning critical infrastructure and communication systems before quantum computers become powerful enough to pose a real threat.
Post-Quantum Cryptography: Building Quantum-Resistant Defenses
To address these challenges, researchers are developing new cryptographic algorithms designed to withstand attacks from both classical and quantum computers. This emerging field is known as post-quantum cryptography (PQC). The goal is to create encryption methods that remain secure even if adversaries have access to advanced quantum machines.
The National Institute of Standards and Technology (NIST) has been leading an international effort to standardize PQC algorithms since 2016 (nist.gov). After several rounds of evaluation, NIST announced its first group of recommended algorithms in 2022. These include lattice-based cryptography, hash-based signatures, and code-based encryption schemes, each offering different trade-offs in terms of speed, security, and implementation complexity.
- Lattice-based cryptography: Relies on hard mathematical problems involving multi-dimensional grids; considered highly resistant to quantum attacks.
- Hash-based signatures: Use cryptographic hash functions for digital signatures; suitable for certain applications but less efficient for general use.
- Code-based encryption: Based on error-correcting codes; offers strong security but can require larger key sizes.
Adopting PQC will require significant updates to software, hardware, and protocols across industries. Many organizations are already testing these new algorithms in pilot projects and preparing for a gradual transition over the next several years.
Preparing for a Quantum Future: Practical Steps and Challenges
Transitioning to quantum-resistant encryption is a complex process that involves technical, organizational, and regulatory hurdles. Companies need to inventory their cryptographic assets, assess which systems are most at risk, and develop migration plans that minimize disruption while maximizing security. This often means running new PQC algorithms alongside existing systems during a transition period, a strategy known as cryptographic agility.
Regulators and industry groups are issuing guidelines to help organizations prepare for the shift. For example, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) recommends that businesses start planning now by identifying critical data assets and engaging with vendors about their post-quantum roadmaps (cisa.gov). Early preparation can help avoid costly last-minute upgrades when quantum computers reach practical utility.
One challenge I’ve observed in conversations with IT leaders is balancing the urgency of quantum threats with ongoing cybersecurity needs. Many organizations already struggle with ransomware, phishing attacks, and compliance requirements. Adding quantum readiness to the mix can feel However, proactive planning (such as updating cryptographic libraries and training staff on PQC concepts) can make the transition smoother when the time comes.
The Broader Impact: Privacy, Policy, and Global Competition
The race for quantum supremacy has geopolitical implications beyond technology alone. Countries see leadership in quantum computing as a strategic advantage that could influence economic power and national security. As a result, governments are investing heavily in research and forming alliances to set standards for post-quantum security.
This competition raises questions about privacy rights and cross-border data flows. If one nation gains early access to powerful quantum decryption tools, it could compromise sensitive communications worldwide. International cooperation will be essential to ensure that new cryptographic standards are robust, transparent, and widely adopted.
On an individual level, consumers may not notice immediate changes as organizations upgrade their security infrastructure behind the scenes. However, staying informed about how personal data is protected (and advocating for transparency from service providers) remains important as technology evolves.
Looking Ahead: Staying Secure in a Quantum Era
While practical quantum computers capable of breaking current encryption are not yet available, the pace of progress suggests it’s only a matter of time before this becomes a reality. The transition to post-quantum cryptography will be one of the most important shifts in cybersecurity over the next decade.
Staying ahead of these changes requires collaboration between researchers, industry leaders, policymakers, and everyday users who rely on secure digital communication. By understanding the risks and preparing now, organizations can safeguard sensitive information against future threats while continuing to benefit from advances in technology.